Internetworking Basics
Networking • Basics
Myself Vikas Singh from Varanasi, Uttar Pradesh. Learning and exploring technical domains at Acharya Institute, Bangalore (IN) from the last two years.
The main goal is to learn as much domains, tool
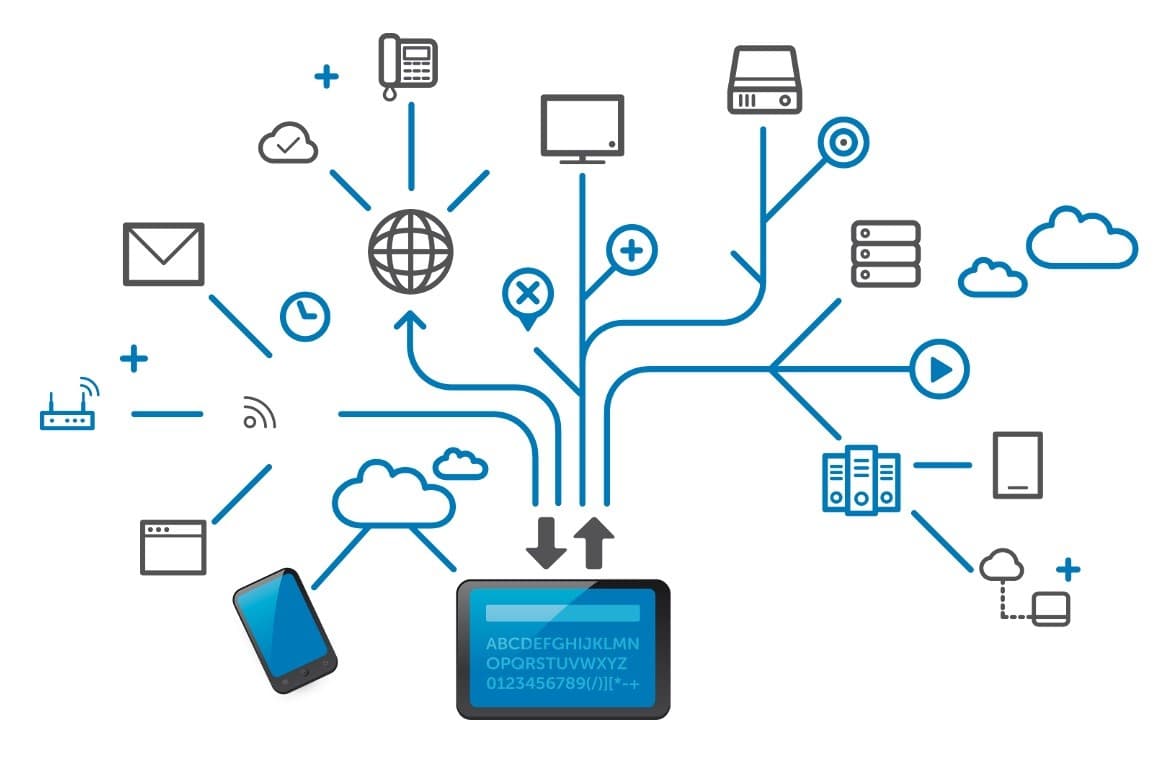
In this section, we'll talk about Internetworking. What is Network? A network is a group of networking devices connected using a router or switch or some other intermediate and other devices like Printers, Scanners, Access Points etc. Group of Networks called the Internet. Let's say Bob wants to talk to Sally. So he has two options whether he yells on the street by her name or find went at his place and knock on his door. In case he yells and communicates with Sally, he'll disturb the other neighbors or it might be possible she lives in another country, town or city or maybe continent so she couldn't hear. And in case they talk to her at her door that'll be a wise decision and they can talk without disturbing others.
Yelling in a public is called Broadcast in networking. Broadcast is nothing but a sender sending the information to everyone. Talking nicely is called Unicast, it is one-to-one communication.
In this scenario there were only two persons to communicate so it was not a big deal...but what if there were are multiple users in a network. Then the yell turns into congestion. To avoid and deal with those congestions there are certain rules and ways. Again, the solution to this problem begins with breaking up a massive network into several smaller ones—something called network segmentation.
Hubs and Switches
In a networking neighborhood environment, all of this infrastructure is managed using devices like routers, switches, and bridges.

We use a switch instead of the hub because hubs don’t segment a network; they just connect network segments
Hub doesn't provide any security but the switch does
Hub broadcast every packet he receives but switch broadcasts the very first packet
The switch has a MAC table hub don't use any MAC table
Switches create separate collision domains with each port.
switches are used to segment networks, but they will not isolate broadcast or multicast packets.
The above figure shows a network that’s been segmented with a switch, making each network segment that connects to the switch its separate collision domain. Doing this results in a lot less yelling! but I want you to make note of the fact that this network is still one, single broadcast domain, meaning that we’ve only decreased our screaming and yelling—not eliminate it. For example, if there’s some sort of vital announcement that everyone in our neighborhood needs to hear about, it will still get loud! You can see that the hub used in Figure just extended the one collision domain from the switch port. The result is that John received the data from Bob but, happily, Sally did not, which is good because Bob intended to talk with John directly. If he had needed to send a broadcast instead, everyone, including Sally, would have received it, possibly causing unnecessary congestion.
List of some of the things that commonly cause LAN traffic congestion:
Too many hosts in a collision domain
Broadcast Storm
Too much multicast traffic
Low bandwidth
Adding hubs for connectivity of the network
A bunch of ARP broadcast
The main purpose of these switches is to make a LAN work better—to optimize its performance—providing more bandwidth for the LAN’s users.
Collision Domain is an Ethernet term used to describe a network scenario in which one device sends a packet out on a network segment and every other device on that same segment is forced to pay attention no matter what. This isn’t very efficient because if a different device tries to transmit at the same time, a collision will occur, requiring both devices to retransmit, one at a time—not good! This happens a lot in a hub environment
Routers

As our planned community starts to grow, we’ll need to add more streets along with traffic control and even some basic security. We achieve this by adding routers because these convenient devices are used to connect networks and route packets of data from one network to another
Routers are employed to efficiently break up a Broadcast Domain*—the set of all devices on a network segment, which is allowed to “hear” all broadcasts sent out on that specific segment.*
If a user wants to communicate in a different network/broadcast domain then the sender needs an address called IP Address to communicate with the receiver.
Used to connect WAN (Wide Area Networks) using Serial Cables.
Routers (layer 3 switches) use logical addressing and provide an important capacity called packet switching
Routers used to break Broadcast Domains as well as collision Domains
Routers filter the traffic based on access-list
Router connects two or more networks using a logical IP Address called internetwork
routers to use a routing table, essentially a map of the internetwork, to make the best path selections for getting data to its proper destination and properly forwarding packets to remote networks
Advantage:
They don't forward broadcast by default.
They can filter the network based on layer 3 (Network layer) information such as an IP address.
Router Functions:
Packet Switching
Packet Filtering
Internetwork Communication
Path Selection
Bridges
Bridges are the same as switches and are used to segment networks, but they will not isolate broadcast or multicast packets. Bridges and switches do the same thing—break up collision domains on a LAN. A switch is just a multiple-port bridge with more brain power. Most bridges have four ports. Which is severely limiting. While switches have variations.
Access Points (APs)
These devices allow wireless devices to connect to a wired network and extend a collision domain from a switch. They’re typically in their broadcast domain or what we’ll refer to as a Virtual LAN (VLAN).
WLAN Controllers
These are the devices that network administrators or network operations centers use to manage access points in medium to large to extremely large quantities. The WLAN controller automatically handles the configuration of wireless access points and was typically used only in larger enterprise systems
Firewalls & IPS

A firewall controls the flow of connections to make the connection more secure. It works on certain security policies. It negotiates the unusual incoming traffic. There are two types of Firewalls:
Traditional Firewalls -
Inspect only network address (IPv4/IPv6) and TCP/UDP port numbers
Based on all forward-or-block decisions based on those values
Next-Generation Firewalls -
Allow deep packet inspection. It inspects every Layer of the OSI Model of every packet.
Ability to block or forward packets based on application awareness. Example: From an enterprise network if someone tries to access Google or FOX news - allow it but block the games and social media sites.
Can utilize the outside service to detect the malicious attacks
IPS Devices are used to detect malicious attacks and viruses at the packet level
CISCO DNA Center -
DNA Stands for Digital Network Architecture
A centralized management dashboard for complete control of a network
Provide a central automation and analytics platform to facilitate "Internet Based Networking" - Managing the network dynamically based on the need of applications.
Appliance pre-built with CISCO DNA Center software
Design your Network
Create topology maps & diagram
Create wireless profiles and SSIDs
Identifying "Golden Images" for software deployments. Golden Images means using the same flavor of OS in all the devices which is bug-free.
Some DNA Center Examples - DN2-HW-APL-XL(Large)
Client & Servers
The client is the device on a network that is used to connect with other devices either host/server to access the resources from the remote device from the internet.
Servers are the most powerful devices as compared to clients in order. Servers are responsible to share the information with the remote devices that request the information and resources.

As we can see here, the user needs information so he will request the server for information and resources. and the server will provide the information. Let's suppose the server is trying to access Google, so he'll request the HTML page of Google using an application to request the server and the server will give him an HTML copy.